KRA19, a captivating system, has gained significant traction within the sphere of data science. Its powerful design allows for remarkable capabilities in sectors such as computer vision. This investigation delves into the core domains of KRA19, unveiling its advantages and potential applications.
- First, we will explore the fundamental principles that underpin KRA19's architecture.
- Secondly, we will investigate the areas of application where KRA19 exhibits its {greatest potential|.
- Finally, we will consider the potential impact of KRA19 on the landscape.
Delving into the Digital Landscape of KRA19.cc, KRA19.at {
The shadowy realm of KRA19.cc and KRA19.at has long captivated researchers and security analysts. These domains, often associated with malicious activities, have become a focal point for investigations into the ever-evolving world of cybercrime.
Deciphering the inner workings of KRA19.cc and KRA19.at requires a multifaceted strategy. It involves examining network traffic, pinpointing vulnerabilities, and partnering with international law enforcement agencies to expose the individuals and organizations behind these domains.
The risks posed by KRA19.cc and KRA19.at are significant. They can range from data breaches to system disruptions. Understanding the threats associated with these domains is crucial for businesses to mitigate risks.
Examining KRA19: A Cybersecurity Perspective
The emergence of advanced cyber threats necessitates a constant adaptation in our cybersecurity strategies. One such threat that has gained significant scrutiny is KRA19, a malicious code with the potential to inflict widespread disruption. Understanding its mechanisms is crucial for effective mitigation. This article delves into the complexities of KRA19, analyzing its capabilities and exploring the best strategies to counteract its influence on individuals and organizations.
A key dimension of KRA19 is its ability to harness existing vulnerabilities in software. By infiltrating these protections, KRA19 can steal sensitive assets. This compromise of data confidentiality can have severe results for both individuals and organizations.
- Furthermore, KRA19's complexity presents a distinct challenge to cybersecurity experts. Its ability to adapt over time, making it complex to detect. This constant shift requires ongoing analysis and the development of new solutions.
Revealing KRA19: The Secret Behind the URLs
KRA19 has become a popular buzzword in recent months. This enigmatic acronym often manifests alongside unusual URLs, leaving many users bewildered. Efforts to decipher the meaning behind KRA19 have been fruitful, adding to its allure and mystery.
- Perhaps KRA19 signifies a specific entity.
- Could it a cutting-edge technology platform?
- Conversely, KRA19 could simply be a misleading tactic.
Despite this of its true nature, KRA19 has undoubtedly capturedour curiosity of a significant number virtual communities.
Unveiling the Mysteries of KRA19: Exploring Uncharted Regions
KRA19 remains a mystery, its true nature shrouded in secrecy. Researchers worldwide are eagerly attempting to penetrate its enigmas. Theories abound, ranging from extradimensional phenomena to extraterrestrial technologies. As we embark deeper into this mysterious territory, the kra19.at possibility of groundbreaking discoveries grows stronger with each passing day.
Unraveling the Mystery of KRA19: A Journey Through Doubt
K unveil a perplexing situation known as KRA19. This intriguing entity has absorbed the attention of many researchers. Its source remain shrouded in ambiguity, leaving a trail of questions in its wake. As we delve deeper into this intricate web of uncertainty, we endeavor to shed light the reality behind KRA19.
Fragments are dispersed throughout a vast landscape, each offering a glimpse of the bigger picture. Yet, the fragments often puzzle rather than construct a unified narrative.
- Conceivably the answer lies in unconventional sources.
- Could it be that KRA19 functions outside the bounds of our current perception?
- Only time will tell
 Hallie Eisenberg Then & Now!
Hallie Eisenberg Then & Now! Jenna Jameson Then & Now!
Jenna Jameson Then & Now!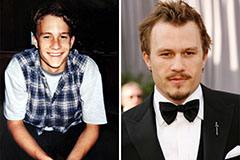 Heath Ledger Then & Now!
Heath Ledger Then & Now! Shane West Then & Now!
Shane West Then & Now! Robin McGraw Then & Now!
Robin McGraw Then & Now!